My problem with Arch Linux
How I fixed a broken GRUB on a fully encrypted Arch Linux disk after a bad config change.
10 posts
How I fixed a broken GRUB on a fully encrypted Arch Linux disk after a bad config change.
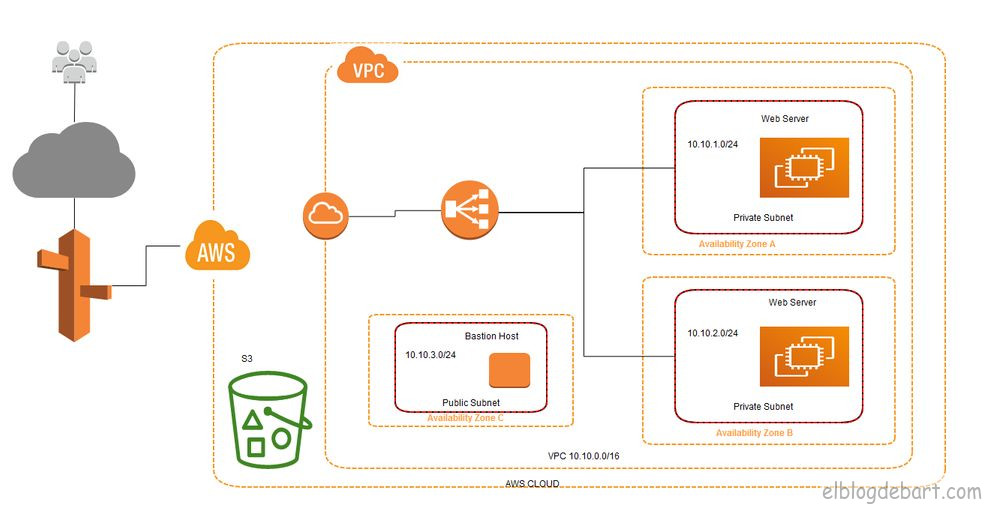
How to deploy a secure VPC on AWS with EC2, Bastion Host, NAT Gateway, and ELB from scratch.

A practical guide to grep with real examples: filtering logs, searching patterns, regex and bash scripting.
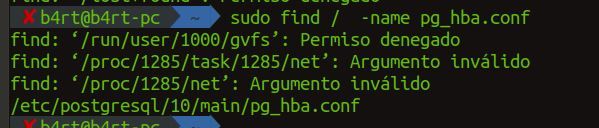
A practical guide to find with real examples: searching by name, type, user, permissions, and executing actions.

A practical Nmap scanning strategy: service fingerprinting, OS detection, timing control, and advanced flags.
A guide to the main Nmap scanning techniques: TCP Connect, SYN, Idle, ACK, X-Mas, and Null scan.

How to install RPM packages with all their dependencies on an internet-restricted CentOS server using repotrack and createrepo.
An introduction to SSH: what it is, how encryption works, and why it replaced Telnet as the standard for remote server management.
How SSH public key authentication works, how to generate ECDSA and RSA key pairs, and how to deploy them to your server securely.
A practical guide to hardening sshd_config: disable root login, enforce key-only auth, restrict users, and tune the most important SSH server settings.