
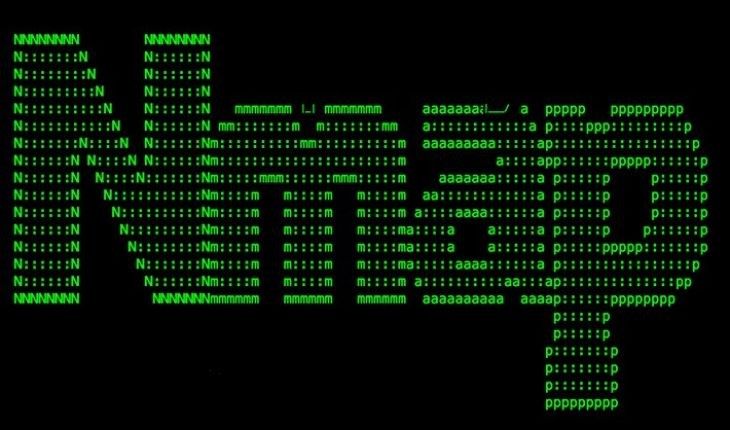
Scanning with Nmap: Gathering Info
A practical Nmap scanning strategy: service fingerprinting, OS detection, timing control, and advanced flags.
5 posts

A practical Nmap scanning strategy: service fingerprinting, OS detection, timing control, and advanced flags.
A guide to the main Nmap scanning techniques: TCP Connect, SYN, Idle, ACK, X-Mas, and Null scan.
An introduction to SSH: what it is, how encryption works, and why it replaced Telnet as the standard for remote server management.
How SSH public key authentication works, how to generate ECDSA and RSA key pairs, and how to deploy them to your server securely.
A practical guide to hardening sshd_config: disable root login, enforce key-only auth, restrict users, and tune the most important SSH server settings.